by Robert Muggah and Marc Goodman*
Digital strikes are already coming hard and fast. In 2018, a massive ransomware attack launched by Iranian hackers shuttered Atlanta’s city hall for five days. This, the largest cyber breach recorded by a US city, disrupted police services, the processing of court cases, payment of parking tickets, business licenses and water bills, and even the nation’s busiest airport. In Baltimore, ransomware attacks in 2018 and 2019 shut down most of the city’s servers and paralyzed its 911 emergency call centre. And it’s not just big US cities on the front-line. Hundreds of smaller ones have paid hundreds of thousands of dollars in bitcoin ransoms to regain access to their own systems, including 22 towns in Texas last month.
The scope of the cyber threat to cities is becoming clearer. According to industry experts, more than 70 percent all reported ransomware attacks in the U.S. target state and local governments. At least 180 public safety call centers were also targeted in the last two years. Cyber criminals are deploying distributed denial of service attacks, ransomware and other off-the-shelf hacker tools to interrupt and burgle municipal networks. Their digital arsenals are sourced from the Deep Web and their weapons are fully automated, meaning attacks can run 24/7. The impacts of the cyber threat should not be taken lightly.
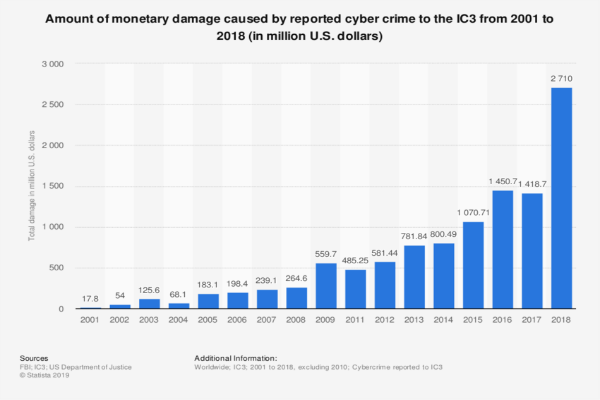
Lloyds estimates that New York city alone could face over $2.3 billion in cyber-related losses in 2020. Given their snowballing deficits, cities can ill afford the burgeoning costs of these digital incursions.
Cyberattacks are not confined to US cities, of course. Virtually all cities large and small have to deal with looming digital disruption. In just the past few year ransomware was used to disrupt the municipal tram system in Dublin, to jam air traffic control and railway ticketing systems in Stockholm, and to shake-down power plants from Johannesburg to Hyderabad. While one might expect these attacks would have set off alarm bells for mayors, city councils and governors, not much has changed.
Why are cities so vulnerable?
One major reason cities have become targets for cybercriminals is because they are lagging far behind the digital revolution. Many of the underlying technologies running their critical infrastructure are outdated. City authorities often lack the skills to upgrade their systems. The brightest minds in tech rarely choose to work for cities, utilities or airports. Instead, they flock to Amazon, Facebook and Google where they earn many times the salary offered in the public sector.
As bad as things are now, technological acceleration could make things dramatically worse. While smart cities, connected homes and intelligent infrastructure will bring certain advantages, their complexity and ubiquity are a hazard for cities.
To date, most city hacks have occurred in “dumb cities”, meaning those that are not yet digitally wired - so imagine the kind of havoc that will ensue when hackers target intelligent transportation networks and traffic flow management systems. In the not so distant future, intelligent roadways - cars that interact with streetlights, ambulances, police cars and fire-trucks - will be widespread. In these environments, cyberattacks won’t just be inconvenient, they will produce pandemonium and ultimately loss of life.
When it comes to digital security, there is very little direction (or funding) being provided by national authorities to nudge states, counties and cities in the right direction. Instead, cities are flooded with technology vendors dressing-up their smart city offerings and touting their economic potential to neighborhoods and residents. There are powerful incentives for them to sell their wares. A study by McKinsey estimated the IoT alone could generate over $11 trillion in economic activity by 2025. In the rush to cash in, private firms are pressing municipalities to build out their infrastructure as quickly as possible but without safeguards to ensure they coexist with existing systems or are regularly updated, patched and protected to the standard required to maintain public safety.
How can cities protect themselves from digital infiltration and disruption?
While traditional crime fighting will continue to demand the attention of leaders and law enforcement agencies, the growth in cyberthreats can no longer be ignored. City and state leaders must adopt a digital security mindset. This means having contingency and disaster plans in place before the next smart-city emergency arises. Just as San Francisco has prepared for earthquakes for decades and Tokyo for tsunamis, so too must cyber-resilience and safety become a core component of disaster response plans for all cities.
Second, city executives have to assume a leadership role in ensuring the digital safety and security of their constituents, and not merely delegate this role to an underling. According to the International City and County Management Association, roughly 60% of municipal technology officials cite a lack of support from their elected officials and top appointees for their city’s poor cybersecurity. Digital security is not only about hardware and software. It is about adopting a comprehensive whole-of-city approach. Security must be conceived as an essential priority, something that is designed into every element of the urban infrastructure, not merely introduced as an afterthought. It requires developing the rules, regulations, procedures and budgets for city authorities, businesses and residents to prepare and respond to digital threats when and after they inevitably occur.
Third, city authorities need to recruit the right personnel. In order to keep cities safe in the 5G era, public sector executives have to attract the right talent - including coders, engineers and cybersecurity experts. The appointment of empowered information security officers is critical, as is ongoing training and research. So too is a return to basics. In nearly all of the cyberattacks against our cities, a common theme repeats itself: human error and a failure to implement acknowledged best practices such as software patching, correct firewall configuration, frequent and redundant backups, and use of multi-factor authentication for logons. The overwhelming majority of attacks could be prevented with these changes alone.
Fourth, cities can go on the offensive and help incubate crowdsourced solutions to real and unexpected security threats. Making data publicly available is the first step; data that scientists, researchers and residents can use to help drive innovation and security in our urban spaces. Helping incentivize competitions and hackathons to develop solutions for expected and unexpected digital challenges are others. Partnerships, including with non-profit groups like Code for America, are worthwhile. So too are ’bug bounty’ programmes that reward ethical hackers who uncover - and report - software security flaws. Crowdsourced cybersecurity and incentive competitions can bring global talent to any municipality, at greatly reduced costs. Supporting digital innovation ecosystems not only bolsters local capacity, it reduces reliance on outside vendors.
Fifth, cities need to initiate a conversation about the kinds of national, state and municipal rules and regulations required to meet the minimum digital security standards with the roll-out of new systems and devices. California recently passed data privacy and digital security legislation requiring all devices sold in the state to possess ’reasonable’ security features designed to prevent unauthorized access, modification, or information disclosure. Cities would do well to share their experiences, but they must also look to the private sector for inspiration. Smart factories, for example, are very careful about protecting their intellectual property, building in systems of control that limit the possibility of technical, and human error and malfeasance. Many of these ideas could useful inform how the connected city secures itself.
As the world hurtles toward a hyper-connected future, some cities will thrive and others will fall behind. Many cities will struggle to pay for digital upgrades and security because they are already freighted with debt and unfunded liabilities. Some cities are (and will be) forced to sell off their public infrastructure at dizzying discounts, depriving the public of fair compensation of their true value. It is likely that large tech firms will play a growing role in privatizing city functions such as digital and physical infrastructure (as Google’s Sidewalk Labs has started doing in Toronto). There is a real possibility that the next generation of cities will be digitally fenced off, designing in security only for those who can afford to live there.
More positively, the rapid spread and lowered cost of new technologies means that some fast-growing cities in emerging markets may benefit from second-mover advantage. Cities across Asia and Africa are already skipping legacy systems - fixed landlines and railways, for example - and leapfrogging to newer, more efficient and cheaper options. Nairobi, for example, has transitioned rapidly to the use of digital currencies such as M-Pesa for its previously unbanked population and has essentially shifted to wireless systems rather than landline phones. The lowered cost of development and deployment mean that more and more cities in emerging economies can potentially avoid making the mistakes of their counterparts, while improving services to their constituents.
Cities need to adjust their priorities to the realities of a networked urban landscape before disaster strikes. While the conveniences of smart cities are enticing, they must be balanced carefully against the known risks. Given the very high likelihood of attack, metropolitan cybersecurity should be a priority for elected officials and policymakers, matched with the resources to build the right protections. Recognizing the precariousness of our situation is the first step. Attracting the best and brightest to public service is essential. So too is a broad discussion about the future security of our cities. The time to protect them is now, before another 50 billion hackable, un-patchable and un-upgradeable devices are added to the world’s digital grid. Because once that happens, there will be few if any options to go back and fix the mistakes we’ve made.
*Principal, SecDev Group and Founder, Future Crimes Institute
**first published in: www.weforum.org




 By: N. Peter Kramer
By: N. Peter Kramer
