by Andrea Bonime-Blanc and Tomer Saban*
In a world of continuous change, challenge and chaos, it is critically important that every organization – from the smallest mom-and-pop business to medium-size nongovernmental organizations (NGO), government agencies and global multinationals – has concrete cyber-crisis readiness plans ready for deployment at any time. Not having this aspect of cyber-resilience in place before the “big” cyber event occurs can become a serious, material or even deadly financial and reputational hit to any entity and its leaders. That has become especially true in this era of multiple cyber and pandemic crises.
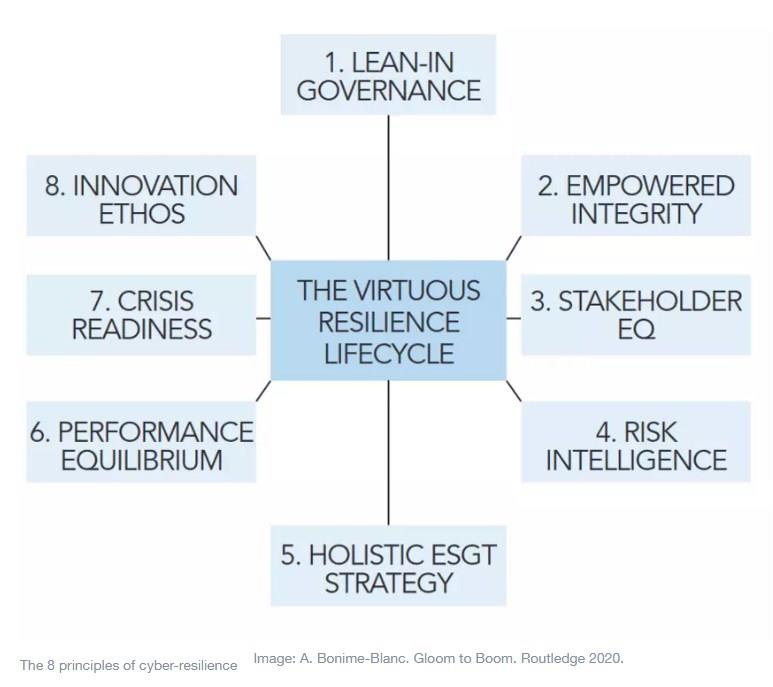
As seen in a recent World Economic Forum piece, there are eight essential elements of building a cyber-resilient organization, as illustrated and summarized in the diagram below:
In this article, we delve more deeply into the nuts and bolts of one of these elements – crisis readiness – as it applies to cyber-risk and security management. We offer five critical aspects of building effective cyber-crisis readiness, the overarching purpose of which is to build, retain and continuously improve organizational cyber-resilience.
Before we outline the five “Ts” of crisis readiness, let’s get our arms around the meaning of “organizational cyber-resilience”. Here is a definition from a 2020 Swiss Re/GEC Risk Advisory White Paper on this topic:
“Cyber-resilience is an organization’s ability to sustainably maintain, build and deliver intended business outcomes despite adverse cyber-events. Organizational practices to achieve and maintain cyber-resilience must be comprehensive and customized to the whole organization (i.e. including the supply chain). They need to include a formal and properly resourced information security program, team and governance that are effectively integrated with the organization’s risk, crisis, business continuity, and education programs.”
— Maya Bundt & Andrea Bonime-Blanc, GEC Risk Advisory
So, in addition to resources, governance and cross-integration with other programmes within an entity (like risk, business continuity and education), effective cyber-crisis preparedness is an essential part of building and maintaining cyber-resilience.
The five “Ts” of organizational cyber-crisis readiness
While the details and tactics of building organizational cyber-crisis readiness will depend on a lot of factors (size, geography, industry, maturity level, diversification, human capital, purpose, complexity, products, services, etc.), there are clear categories of actions that any entity should take that are customized to that entity and its purpose and portfolio. These are the five “T’s” of cyber-crisis readiness:
1. Talent & planning
The most essential component of cyber resilience (and cyber-crisis readiness specifically) is to have the right people preparing by sitting around the virtual or actual table, rehearsing for actual cyber crises and dealing with them when they come.
A well-formed crisis management team and plan will consist of:
-Specified individuals, including from the highest level of the organization, and including a liaison to the board or other oversight body
-A crisis-management team leader and a backup leader as well as alternates to the main core group members
-Regular meetings of the team (principals and alternates) to compare notes, review, update, revise protocols and engage in scenario exercises
-A customized crisis-management plan, no matter how simple, with details about the who, what, when, why and how of a crisis
-A key, high-level team member with knowledge and visibility of the digital and technological footprint of the organization and its information security and business continuity systems, like a chief information security officer or similar
2. Technology & infosec governance
It is critical for an organization to have determined its overall technology and information security (infosec) governance approach – in other words there needs to be a method to the madness of how an organization determines, protects and runs interference on all things digital within its footprint.
This would include connecting the dots and having an overall philosophy determined at the highest levels of the organization (including the board and management) on how to deal with overarching data, infosec and cybersecurity governance, as well as linking crisis management to the following:
-IT systems support
-Human resources and travel protocols
-Data protection and retrieval
-Accounting and finance systems
-Legal and regulatory issues, requirements and implications
-Facilities management
3. Training & communication
An entity – regardless of size – must have some form of cyber-hygiene education plan in place where testing of the system and teaching of staff and third parties about the “do’s and don’ts” is critical and always ongoing.
Training and preparedness need to extend to all corners of the organization from the very top (the board should be informed and trained regularly on the entity’s cyber-resilience) to the latest recruits, and across all disciplines, functions, operations, sub-entities and far-reaching locations. Moreover, crisis-preventing cyber-hygiene training and communications should extend to the supply chain ecosystem of an entity as well, since so much of the cyber-threat matrix enters an entity’s domain through third parties.
4. Technology tools
As the people, governance, training and communications pieces of a cyber-crisis plan take shape, it is critically important that the team and the plan have the right insight into and mapping of all the necessary and desirable technology tools deployed throughout the organization – both in advance of a major cyber-crisis and for purposes of maintaining post-crisis business continuity.
When looking at security tools that should be in place, there are three key concepts to consider: visibility, simplicity and automation.
-Visibility. As the saying goes: “You can’t protect what you can’t see.”
It is critical that an organization be able to constantly monitor its cyber environment and quickly move from a bird’s eye view into the specific actions that have happened.
-Simplicity. We are living in a challenging time where skilled security personnel are in very high demand and entry-level personnel need to use tools that enable them to perform at more experienced analyst levels, especially when there is a serious cyber breach.
-Automation. It is critical to having an effective incident response plan. With the propagation of so many security tools, it is no wonder that analysts are overwhelmed with more alerts than ever before. Manual tasks and repetitive work should be effortlessly completed with an effective automation program that frees infosec personnel to focus on the real threats and on proactive threat hunting.
5. Triangulation & continuous improvement
Finally, there is a series of important system-wide practices and policies that need to be part of the cyber-crisis readiness approach of every entity that helps to triangulate (identify, mitigate and solve) problems preferably before they happen but often after the fact as well. They include:
-A robust and agile enterprise risk-management programme that seamlessly incorporates cyber-risk issues
-A likewise robust auditing and evaluation system – with both internal and external experts – who can deploy, read and interpret information security and related concerns, gaps and problems before they become too large
-A deliberate and concrete continuous improvement system embedded into the entity where lessons learned from past mistakes are deeply analyzed and utilized to integrate improvements into the risk and security profile of the entity
We believe that businesses, NGOs, government agencies and other types of organizations will truly benefit from this systematic approach to building a deliberate cyber-crisis-ready approach. In this way, the worst of the downsides of a cyber attack can be mitigated and maybe even thwarted because of the coordinated and seamless approach of the internal team and their external experts, infosec governance, and the technology tools deployed to build sustainable cyber-resilience.
*Founder and CEO, GEC Risk Advisory and CEO, WireX Systems
**first published in: www.weforum.org




 By: N. Peter Kramer
By: N. Peter Kramer
