by Sebastian Banescu, Ben Borodach and Ashley Lannquist*
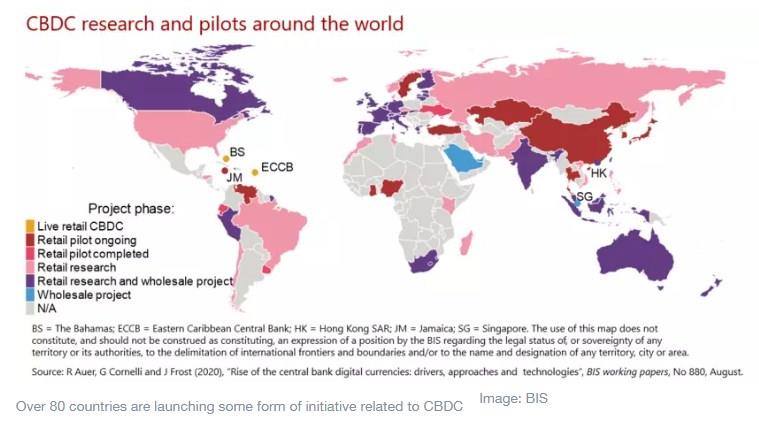
With G7 officials recently endorsing principles for central bank digital currencies (CBDC), and over 80 countries launching some form of initiative related to CBDC, it seems their widespread deployment is a matter of time. CBDC is a digital form of central bank money that can be accessible to the general public; essentially, it consists of individuals and firms having access to transaction and savings accounts with their home country’s central bank. Those of the Bahamas, China and Nigeria have all implemented early CBDC programmes, with more expected in the future. If successful, CBDC could help policy-makers achieve goals around payment efficiency, financial inclusion, banking and payment competitiveness, access to safe central bank money in the era of digital payments, and more.
Yet like any digital payment system, CBDC is vulnerable to cybersecurity attack, account and data breaches and theft, counterfeiting, and even farther-off challenges related to quantum computing. For citizens to be comfortable adopting CBDC, they will need to be confident in its security. Ultimately, it will not be successful if it does not carefully consider and invest in a robust cybersecurity strategy. Decision-makers should look to cybersecurity best practices such as those published by the US National Institute of Standards and Technology (NIST) and the Microsoft “STRIDE” model. This article, which summarizes key points from the World Economic Forum’s new white paper on CBDC Technology Considerations, lays out additional imperative considerations for CBDC cybersecurity.
How can we make sure CBDC is secure for decades to come? We discuss four major dimensions to its cybersecurity below:
1. Credential theft and loss
CBDC access credentials are needed for accessing and transferring funds. Such credentials could be given in the form of a passphrase that could be easily communicated even on paper, or a hardware token that stores the private keys. Regardless of the form, the threat of theft and credential loss is significant, meaning account funds and data could be compromised.
Theft can be physical or virtual, especially in the case of passphrases. Given the arsenal of modern attackers, techniques such as social engineering, side-channel attacks and malware could be used to extract credentials from a CBDC user’s device. Moreover, if passphrases or hardware tokens are lost/damaged due to fire/water or natural calamities, CBDC users should not simply lose all their funds and data. Therefore, the system should have built-in credential recovery mechanisms.
If a CBDC is based on blockchain technology, it might use a multi-signature (“multi-sig”) wallet where at least two other trusted parties hold credentials to the same wallet (this could be the central bank itself and/or family members or other contacts of the end users). The drawback of multi-sig wallets is that they are less user-friendly, since for any transfer one needs to coordinate with at least one other party. Such security-usability trade-offs are common even nowadays with internet banking where 2 Factor Authentication (2FA) is extremely common. If CBDC is based on traditional technology, a privileged authority could simply update a database entry with new credentials.
2. Users with privileged roles
One concern is that central bank or government insiders, law enforcement and other agents may have roles that allow privileged actions, such as the freezing or withdrawal of funds in CBDC accounts without the user’s consent. These capabilities are in line with today’s compliance procedures in regulated payment systems. Though such roles are likely to be a functional requirement of a CBDC, it is possible for them to enable malicious insiders to abuse the system. As with other types of information security, the central bank – and any intermediaries involved – should have and execute a cybersecurity risk-management plan covering such privileges. Multi-party mechanisms, such as those employed by multi-signature wallets or other protections, could increase the difficulty of such attacks.
If the CBDC operates on blockchain technology, where nodes include non-central bank entities that have powers to validate or invalidate transactions, malicious validator nodes can pose security threats. They could also undermine the central bank’s monetary authority and independence by virtue of accepting or rejecting transactions that are contrary to the central bank’s intention. Thus, it is generally not recommended for non-central bank nodes to have transaction validation powers unless absolutely necessary.
3. System integrity and “double spending”
Depending on the consensus protocol used, non-central bank nodes with privileged power could declare transactions as invalid, essentially blocking them from being accepted by the network and creating a denial-of-service attack for CBDC users and censorship of their transactions.
Collusion by non-central bank nodes could also enable “double-spending” attacks, a form of counterfeiting where the CBDC is spent multiple times illegitimately. The nodes may also decide to “fork” the distributed ledger, creating a different track and view of the ledger of transactions that disagrees with the central bank’s. CBDC end users could try to spend funds from their wallets in multiple places, also constituting digital counterfeiting. Risk of double-spend is higher if the CBDC in question has offline capability, depending on the technology with which it operates; in this scenario, double-spend transactions could be sent to offline entities without the high-security validation process that would normally occur online.
By imposing spending limits and transaction frequency when the CBDC user is offline, the impact of such attacks would be reduced. Further, once a device that is conducting transactions comes back “online”, compliance software could sync with any transactions that have concurred during the offline period.
4. Quantum computing
Quantum computing will ultimately impact all financial services as it compromises major data encryption methodologies and cryptographic primitives used for protecting access, confidentiality and integrity of data stored and transmitted. CBDC is no exception. Therefore, the threat of emerging quantum computers, which can compromise the cryptography employed to secure CBDC accounts, must be taken into account during technology design. For instance, central banks should consider the vulnerability of certain primitives to forthcoming quantum computing. Moreover, quantum computers in the future might be able to break the cryptography in the CBDC system without detection.
Cybersecurity, along with technical resilience and sound technical governance, are the most important elements of CBDC technical design. Failure to implement a robust cybersecurity strategy and consider the risks introduced above could compromise citizen data and funds, the success of the CBDC programme, central bank reputational risk and broader opinions of the new currency. Based on past experiences in cybersecurity failures, the bar for security is not only about “keeping the bad guys out” or minimizing unauthorized account access. It must be comprehensive and consider the full spectrum of risks, ensuring that the system works as it was designed and that its integrity remains intact. Only then will CBDC be successful in achieving its goals.
*Senior Research Engineer / Security Auditor, Quantstamp and Vice-President, Strategy and Operations, Team8 and Project Lead, Blockchain and Distributed Ledger Technology, World Economic Forum
**first published in: www.weforum.org




 By: N. Peter Kramer
By: N. Peter Kramer
